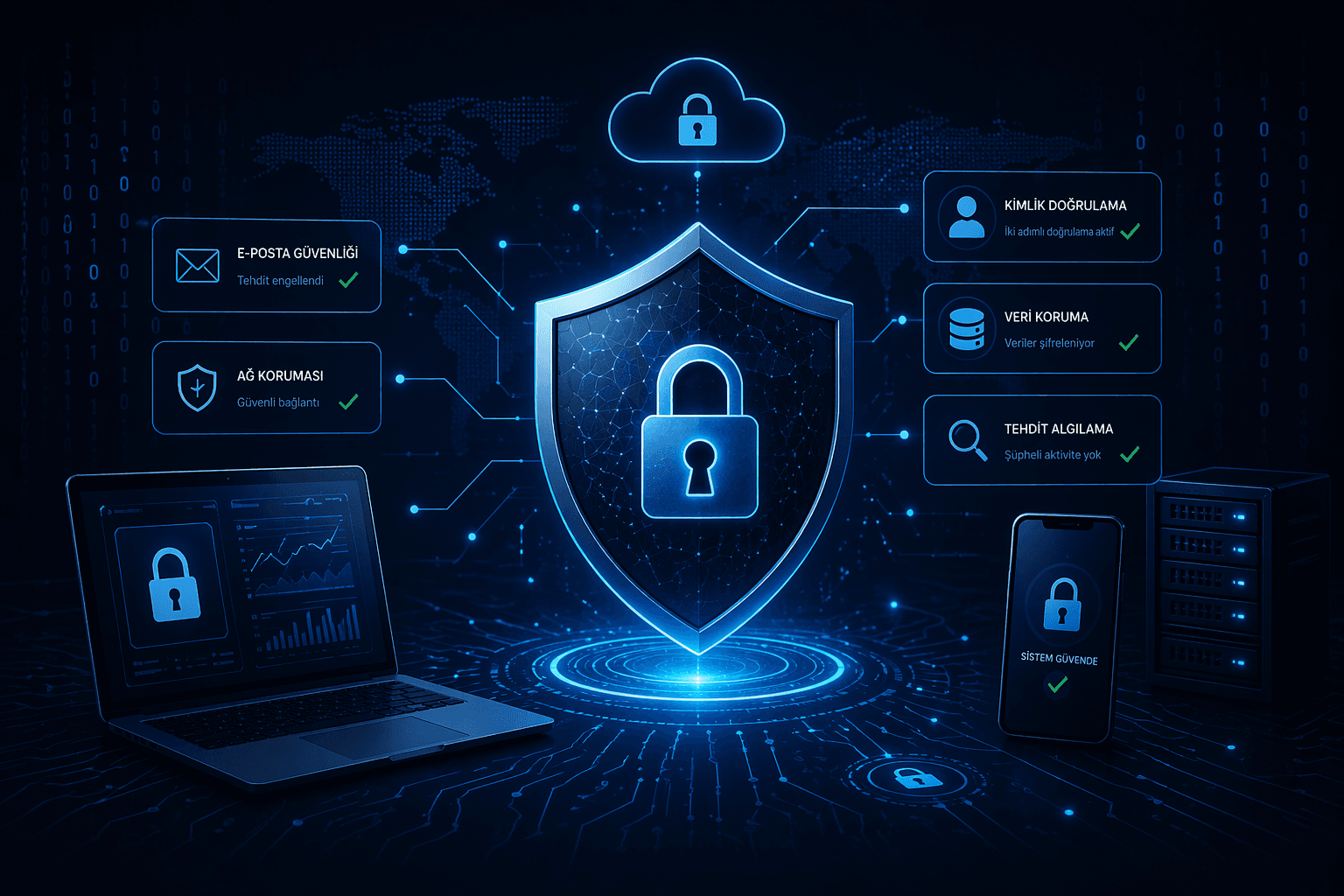
Enterprise Cyber Security and Protection Infrastructure
This project is a comprehensive security solution covering penetration tests, vulnerability scans, access control mechanisms and continuous monitoring systems to improve the security of enterprise digital infrastructure.
Project planning and development process
Every project is handled holistically with needs analysis, experience design, technical development and a sustainability approach.
Reconnaissance and information gathering
Passive and active information gathering techniques are used to identify open ports, services and potential attack surfaces.
Vulnerability analysis
Automated and manual testing methods are used to identify security weaknesses in the system.
Penetration testing
Real attack scenarios are simulated to test risks such as unauthorized access, data leakage and system compromise.
Reporting and remediation guidance
All detected vulnerabilities are reported in detail and technical or operational remediation suggestions are provided.
